Trezor Login: Your Gateway to Secure Crypto
Discover how to access your Trezor wallet safely, manage your crypto assets effectively, and maintain top-level security with each login.
Why Trezor Login is Crucial
Logging in to your Trezor wallet is not just about accessing your funds—it's the first line of defense against cyber threats. Trezor combines hardware-level PIN entry with offline private key storage, providing unmatched protection compared to typical hot wallets.
Always ensure you use the official Trezor Suite or the verified Trezor website. Avoid clicking links from unknown emails or messages, as phishing attempts are a major threat in the crypto space.
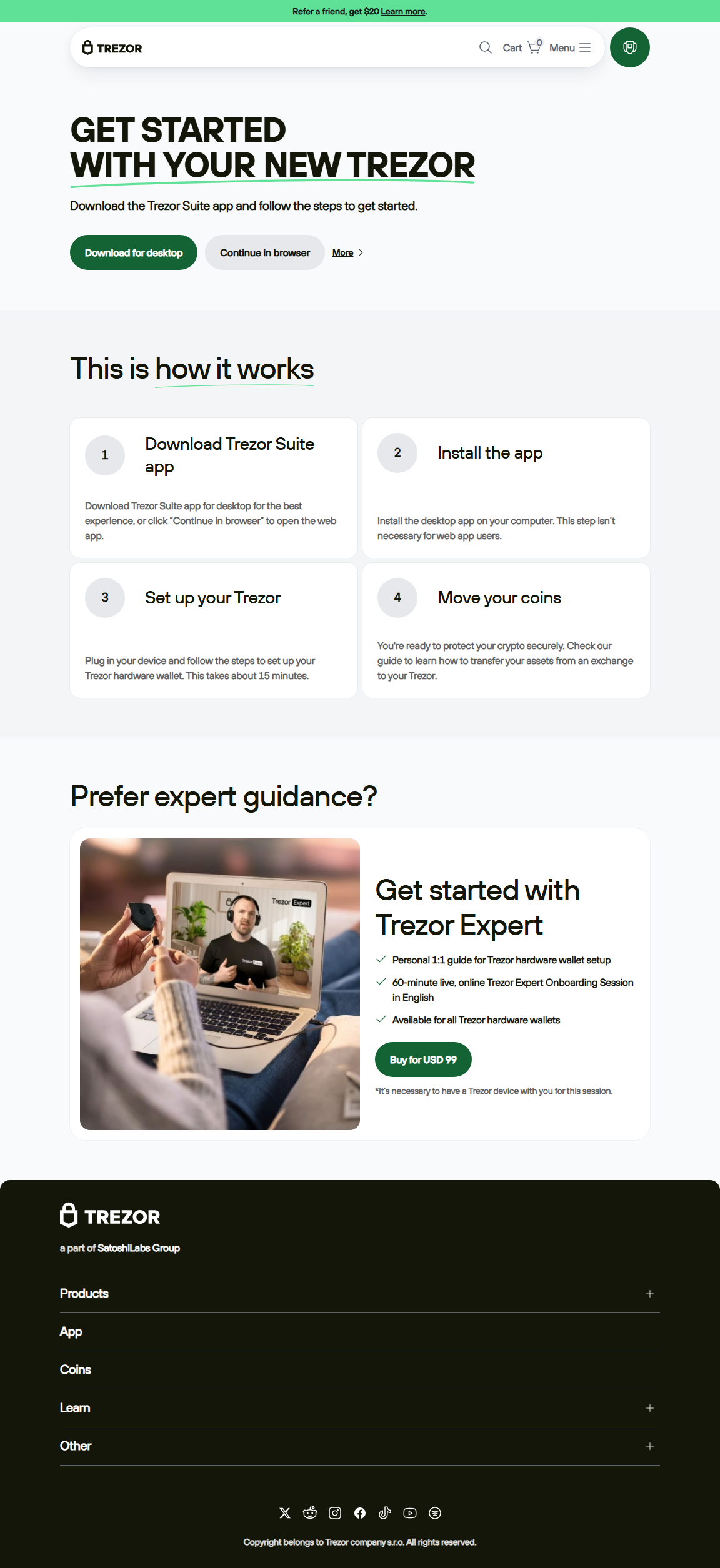
Step-by-Step Login Guide
Step 1: Launch Trezor Suite or Web Wallet
Always access your wallet through official channels. Typing trezor.io manually or opening Trezor Suite ensures you avoid fraudulent sites.
Step 2: Connect Your Trezor Device
Plug your Trezor into a secure USB port. Verify that the device is authentic and firmware is up to date before proceeding.
Step 3: Enter PIN
Input the PIN on the device itself. This prevents keyloggers or malware from capturing your credentials.
Step 4: Access Wallet Dashboard
After verification, your wallet opens, allowing you to view balances, send crypto, and manage your portfolio securely.
Essential Security Tips for Login
- Always use official links: Avoid third-party URLs.
- Keep firmware updated: Latest updates prevent vulnerabilities.
- Never share PIN: Your PIN is private and should never be revealed.
- Secure recovery seed: Store offline in a safe location.
- Enable additional security layers: Use 2FA or passphrase protection if available.
Trezor Login vs Software Wallets
| Feature | Trezor | Software Wallets |
|---|---|---|
| Security | Offline private key storage | Keys online, prone to hacking |
| Accessibility | Requires device connection | Accessible from any device |
| Control | Full control over private keys | Keys may be partially managed by provider |
| Ideal For | Long-term, high-value storage | Frequent, low-value transactions |
"Logging into your Trezor wallet the right way is the first step to ensuring your crypto remains secure and fully under your control."
Frequently Asked Questions
What if I forget my Trezor PIN?
Reset your device using the recovery seed. Keep the seed stored securely offline.
Can I log in from multiple computers?
Yes, but each login requires the Trezor device and PIN entry. Private keys never leave the device.
Is public computer login safe?
While safer than software wallets, avoid public computers due to possible malware or keyloggers.
Do I need internet for Trezor login?
Internet is required for Trezor Suite functionality, but private keys remain offline for maximum security.
Access Your Trezor Wallet Safely Today
By following secure login steps and using official Trezor tools, you can confidently manage your crypto portfolio while keeping your assets protected at all times.